Security Is Our Foundation
Enterprise-grade security infrastructure built for Wall Street's most demanding requirements. Every layer of our platform is engineered to protect your most sensitive financial data.
Independently Verified Security
Our security posture is validated by the industry's most rigorous independent audits and certifications.
SOC 2 Type II
Independently audited controls for security, availability, processing integrity, confidentiality, and privacy. Our SOC 2 Type II report demonstrates sustained compliance over time, not just a point-in-time snapshot.
SOC 1
Independently audited internal controls over financial reporting. Our SOC 1 report provides assurance that Loffa's settlement and compliance processes meet the standards required by our clients' financial auditors.
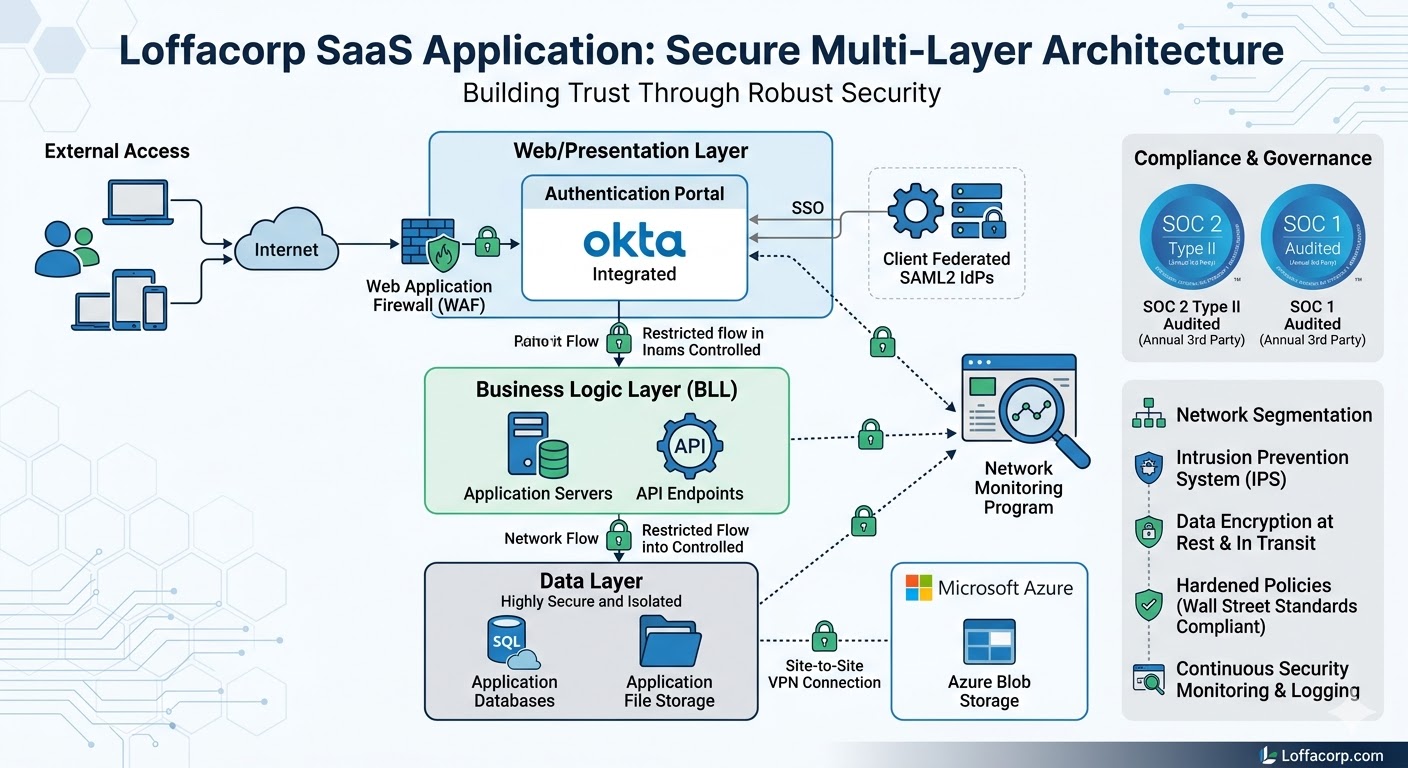
Multi-Layer Security Architecture
Our platform employs a defense-in-depth strategy with multiple overlapping security layers. Each ring of protection operates independently, ensuring that no single point of failure can compromise your data.
- Perimeter Security — Web application firewalls, DDoS protection, and intrusion detection
- Network Security — Encrypted tunnels, network segmentation, and micro-segmentation
- Application Security — Secure SDLC, code review, and penetration testing
- Data Security — AES-256 encryption at rest, TLS 1.3 in transit, tokenization
Enterprise-Grade Data Centers
Your data is housed in the world's most secure facilities with multi-cloud redundancy and geographic distribution.
Iron Mountain Data Centers
Primary hosting in Iron Mountain's underground, nuclear-hardened facilities. Biometric access, 24/7 armed security, and advanced environmental controls protect physical infrastructure.
Microsoft Azure Cloud
Cloud infrastructure powered by Microsoft Azure with enterprise-grade SLAs, geo-redundant storage, and built-in compliance controls for financial services workloads.
AWS Backup & DR
Geographically distributed disaster recovery on Amazon Web Services ensures business continuity. Automated failover, real-time replication, and sub-hour RPO/RTO targets.
24/7 Surveillance
Round-the-clock security monitoring with real-time alerting, automated threat response, and a dedicated Security Operations Center staffed by certified analysts.
99.99% Uptime SLA
Guaranteed availability backed by redundant power, networking, and compute resources. Automated failover ensures uninterrupted access to critical settlement workflows.
Multi-Region Redundancy
Data replicated across multiple geographic regions ensures resilience against regional outages. Automatic traffic routing directs users to the nearest healthy data center.
Comprehensive Security Controls
Rigorous policies and technical controls ensure your data is protected at every level of our operations.
Access Management
Role-based access control (RBAC) with least-privilege principles. Multi-factor authentication, SSO integration, and comprehensive audit trails for every access event.
Encryption
AES-256 encryption for data at rest and TLS 1.3 for data in transit. Hardware security modules (HSMs) manage cryptographic keys with FIPS 140-2 Level 3 validation.
Continuous Monitoring
Real-time security information and event management (SIEM) with machine-learning-driven anomaly detection. Continuous vulnerability scanning and automated compliance reporting.
Incident Response
Documented incident response plan with defined escalation paths and communication protocols. Regular tabletop exercises and post-incident reviews ensure continuous improvement.
Vendor Management
Rigorous third-party risk assessment program with ongoing monitoring of vendor security postures. All sub-processors undergo annual security reviews and contractual obligations.
Regulatory Compliance
Purpose-built for SEC, FINRA, and DTCC regulatory requirements. Automated compliance workflows ensure adherence to evolving financial industry regulations.
Ready to See Our Security in Action?
Schedule a security briefing with our team. We'll walk you through our architecture, certifications, and how we protect the world's largest financial institutions.